Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
Displaying 10 of 62 results control clear search
Urban Dynamics
Hideyuki Nagai | Published Monday, November 11, 2019This is an urban dynamics ABM of abstraction of a city and residents’ activities there.
It allows you to evaluate the effects of urban policies, such as an introduction of an open facility for residents with pedestrian-friendly accommodations, promotion of bicycle use, and control of private automobile use in an urban central area, in controlling urban sprawl.
00b SimEvo_V5.08 NetLogo
Garvin Boyle | Published Saturday, October 05, 2019In 1985 Dr Michael Palmiter, a high school teacher, first built a very innovative agent-based model called “Simulated Evolution” which he used for teaching the dynamics of evolution. In his model, students can see the visual effects of evolution as it proceeds right in front of their eyes. Using his schema, small linear changes in the agent’s genotype have an exponential effect on the agent’s phenotype. Natural selection therefore happens quickly and effectively. I have used his approach to managing the evolution of competing agents in a variety of models that I have used to study the fundamental dynamics of sustainable economic systems. For example, here is a brief list of some of my models that use “Palmiter Genes”:
- ModEco - Palmiter genes are used to encode negotiation strategies for setting prices;
- PSoup - Palmiter genes are used to control both motion and metabolic evolution;
- TpLab - Palmiter genes are used to study the evolution of belief systems;
- EffLab - Palmiter genes are used to study Jevon’s Paradox, EROI and other things.
…
Peer reviewed COMMAND-AND-CONTROL
Farzaneh Davari | Published Tuesday, September 10, 2019 | Last modified Thursday, September 12, 2019The command and control policy in natural resource management, including water resources, is a longstanding established policy that has been theoretically and practically argued from the point of view of social-ecological complex systems. With the intention of making a system ecologically resilient, these days, policymakers apply the top-down policies of controlling communities through regulations. To explore how these policies may work and to understand whether the ecological goal can be achieved via command and control policy, this research uses the capacity of Agent-Based Modeling (ABM) as an experimental platform in the Urmia Lake Basin (ULB) in Iran, which is a social-ecological complex system and has gone through a drought process.
Despite the uncertainty of the restorability capacity of the lake, there has been a consensus on the possibility to artificially restore the lake through the nationally managed Urmia Lake Restoratoin Program (ULRP). To reduce water consumption in the Basin, the ULRP widely targets the agricultural sector and proposes the project of changing crop patterns from high-water-demand (HWD) to low-water-demand (LWD), which includes a component to control water consumption by establishing water-police forces.
Using a wide range of multidisciplinary studies about Urmia Lake at the Basin and sub-basins as well as qualitative information at micro-level as the main conceptual sources for the ABM, the findings under different strategies indicate that targeting crop patterns change by legally limiting farmers’ access to water could force farmers to change their crop patterns for a short period of time as long as the number of police constantly increases. However, it is not a sustainable policy for either changing the crop patterns nor restoring the lake.
Peer reviewed Organizational behavior in the hierarchy model
Smarzhevskiy Ivan | Published Tuesday, June 18, 2019 | Last modified Wednesday, July 31, 2019In a two-level hierarchical structure (consisting of the positions of managers and operators), persons holding these positions have a certain performance and the value of their own (personal perception in this, simplified, version of the model) perception of each other. The value of the perception of each other by agents is defined as a random variable that has a normal distribution (distribution parameters are set by the control elements of the interface).
In the world of the model, which is the space of perceptions, agents implement two strategies: rapprochement with agents that perceive positively and distance from agents that perceive negatively (both can be implemented, one of these strategies, or neither, the other strategy, which makes the agent stationary). Strategies are implemented in relation to those agents that are in the radius of perception (PerRadius).
The manager (Head) forms a team of agents. The performance of the group (the sum of the individual productivities of subordinates, weighted by the distance from the leader) varies depending on the position of the agents in space and the values of their individual productivities. Individual productivities, in the current version of the model, are set as a random variable distributed evenly on a numerical segment from 0 to 100. The manager forms the team 1) from agents that are in (organizational) radius (Op_Radius), 2) among agents that the manager perceives positively and / or negatively (both can be implemented, one of the specified rules, or neither, which means the refusal of the command formation).
Agents can (with a certain probability, given by the variable PrbltyOfDecisn%), in case of a negative perception of the manager, leave his group permanently.
It is possible in the model to change on the fly radii values, update the perception value across the entire population and the perception of an individual agent by its neighbors within the perception radius, and the probability values for a subordinate to make a decision about leaving the group.
You can also change the set of strategies for moving agents and strategies for recruiting a team manager. It is possible to add a randomness factor to the movement of agents (Stoch_Motion_Speed, the default is set to 0, that is, there are no random movements).
…
FoxNet is an individual-based modelling framework that can be customised to generate high-resolution red fox Vulpes vulpes population models for both northern and southern hemispheres. FoxNet predicts red fox population dynamics, including responses to control and landscape productivity. Model landscapes (up to ~15,000 km^2 and bait layouts can be generated within FoxNet or imported as GIS layers.
If you use FoxNet, please cite:
Hradsky BA, Kelly L, Robley A, Wintle BA (in review). FoxNet: an individual-based modelling framework to support red fox management. Journal of Applied Ecology.
The impact of potential crowd behaviours on emergency evacuation: an evolutionary game theoretic approach
Azhar Mohd Ibrahim | Published Monday, July 30, 2018Crowd dynamics have important applications in evacuation management systems relevant to organizing safer large scale gatherings. For crowd safety, it is very important to study the evolution of potential crowd behaviours by simulating the crowd evacuation process. Planning crowd control tasks by studying the impact of crowd behaviour evolution towards evacuation could mitigate the possibility of crowd disasters. During a typical emergency evacuation scenario, conflict among agents occurs when agents intend to move to the same location as a result of the interaction with their nearest neighbours. The effect of the agent response towards their neighbourhood is vital in order to understand the effect of variation of crowd behaviour on the whole environment. In this work, we model crowd motion subject to exit congestion under uncertainty conditions in a continuous space via computer simulations. We model best-response, risk-seeking, risk-averse and risk-neutral behaviours of agents via certain game theoretic notions. We perform computer simulations with heterogeneous populations in order to study the effect of the evolution of agent behaviours towards egress flow under threat conditions. Our simulation results show the relation between the local crowd pressure and the number of injured agents. We observe that when the proportion of agents in a population of risk-seeking agents is increased, the average crowd pressure, average local density and the number of injured agents increases. Besides that, based on our simulation results, we can infer that crowd disasters could be prevented if the agent population consists entirely of risk-averse and risk-neutral agents despite circumstances that lead to threats.
Potato late blight model
Francine Pacilly | Published Friday, April 13, 2018The purpose of the model is to simulate the spatial dynamics of potato late blight to analyse whether resistant varieties can be used effectively for sustainable disease control. The model represents an agricultural landscape with potato fields and data of a Dutch agricultural region is used as input for the model. We simulated potato production, disease spread and pathogen evolution during the growing season (April to September) for 36 years. Since late blight development and crop growth is weather dependent, measured weather data is used as model input. A susceptible and late blight resistant potato variety are distinguished. The resistant variety has a potentially lower yield but cannot get infected with the disease. However, during the growing season virulent spores can emerge as a result of mutations during spore production. This new virulent strain is able to infect the resistant fields, resulting in resistance breakdown. The model shows how disease severity, resistance durability and potato yield are affected by the fraction of fields across a landscape with a disease-resistant potato variety.
Peer reviewed Population Genetics
Kristin Crouse | Published Thursday, February 08, 2018 | Last modified Wednesday, September 09, 2020This model simulates the mechanisms of evolution, or how allele frequencies change in a population over time.
Simulation of the Governance of Complex Systems
Fabian Adelt Johannes Weyer Robin D Fink Andreas Ihrig | Published Monday, December 18, 2017 | Last modified Friday, March 02, 2018Simulation-Framework to study the governance of complex, network-like sociotechnical systems by means of ABM. Agents’ behaviour is based on a sociological model of action. A set of basic governance mechanisms helps to conduct first experiments.
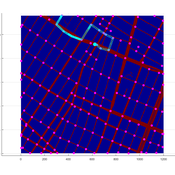
Agent-based model of WiFi tracking system in urban environment
Christopher Thron Khoi Tran | Published Friday, April 21, 2017This code simulates the WiFi user tracking system described in: Thron et al., “Design and Simulation of Sensor Networks for Tracking Wifi Users in Outdoor Urban Environments”. Testbenches used to create the figures in the paper are included.
Displaying 10 of 62 results control clear search