About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 549 results for "Viet Cao" clear search
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
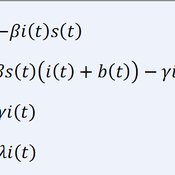
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
Potato late blight model
Francine Pacilly | Published Friday, April 13, 2018The purpose of the model is to simulate the spatial dynamics of potato late blight to analyse whether resistant varieties can be used effectively for sustainable disease control. The model represents an agricultural landscape with potato fields and data of a Dutch agricultural region is used as input for the model. We simulated potato production, disease spread and pathogen evolution during the growing season (April to September) for 36 years. Since late blight development and crop growth is weather dependent, measured weather data is used as model input. A susceptible and late blight resistant potato variety are distinguished. The resistant variety has a potentially lower yield but cannot get infected with the disease. However, during the growing season virulent spores can emerge as a result of mutations during spore production. This new virulent strain is able to infect the resistant fields, resulting in resistance breakdown. The model shows how disease severity, resistance durability and potato yield are affected by the fraction of fields across a landscape with a disease-resistant potato variety.
CITMOD A Tax-Benefit Modeling System for the average citizen
Philip Truscott | Published Monday, August 15, 2011 | Last modified Saturday, April 27, 2013Must tax-benefit policy making be limited to the ‘experts’?
How to not get stuck – an ant model showing how negative feedback due to crowding maintains flexibility in ant foraging
Tomer Czaczkes | Published Thursday, December 17, 2015Positive feedback can lead to “trapping” in local optima. Adding a simple negative feedback effect, based on ant behaviour, prevents this trapping
Product Diffusion Model in an Advance Selling Strategy
Peng Shao | Published Tuesday, March 15, 2016 | Last modified Tuesday, March 15, 2016the model can be used to describe the product diffusion in an Advance Selling Strategy. this model takes into account the consumers product adoption, and describe consumer’s online behavior based on four states.
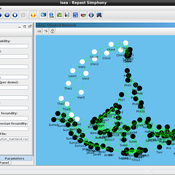
Modeling Asian-Papuan Admixture during the Neolithic Expansion across Island Southeast Asia
Murray Cox François Vallée | Published Friday, December 09, 2016This Repast Simphony model simulates genomic admixture during the farming expansion of human groups from mainland Asia into the Papuan dominated islands of Southeast Asia during the Neolithic period.
04 TpLab V2.08 – Teleological Pruning Laboratory
Garvin Boyle | Published Saturday, April 15, 2017Our societal belief systems are pruned by evolution, informing our unsustainable economies. This is one of a series of models exploring the dynamics of sustainable economics – PSoup, ModEco, EiLab, OamLab, MppLab, TpLab, CmLab.
COOPER - Flood impacts over Cooperative Winemaking Systems
David Nortes Martinez David Nortes-Martinez | Published Thursday, February 08, 2018 | Last modified Friday, March 22, 2019The model simulates flood damages and its propagation through a cooperative, productive, farming system, characterized as a star-type network, where all elements in the system are connected one to each other through a central element.
Displaying 10 of 549 results for "Viet Cao" clear search