About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 1123 results for "Bin-Tzong Chi" clear search
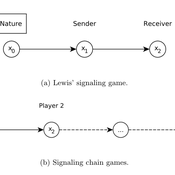
Lewis' Signaling Chains
Giorgio Gosti | Published Wednesday, January 14, 2015 | Last modified Friday, April 03, 2015Signaling chains are a special case of Lewis’ signaling games on networks. In a signaling chain, a sender tries to send a single unit of information to a receiver through a chain of players that do not share a common signaling system.
Success bias imitation increases the probability of effectively dealing with ecological disturbances
Jacopo A. Baggio Vicken Hillis | Published Thursday, April 13, 2017 | Last modified Thursday, August 02, 2018This model aims to investigate how different type of learning (social system) and disturbance specific attributes (ecological system) influence adoption of treatment strategies to treat the effects of ecological disturbances.
Pedestrian model
Gudrun Wallentin Dana Kaziyeva Martin Loidl Petra Stutz | Published Monday, August 07, 2023The model generates disaggregated traffic flows of pedestrians, simulating their daily mobility behaviour represented as probabilistic rules. Various parameters of physical infrastructure and travel behaviour can be altered and tested. This allows predicting potential shifts in traffic dynamics in a simulated setting. Moreover, assumptions in decision-making processes are general for mid-sized cities and can be applied to similar areas.
Together with the model files, there is the ODD protocol with the detailed description of model’s structure. Check the associated publication for results and evaluation of the model.
Installation
Download GAMA-platform (GAMA1.8.2 with JDK version) from https://gama-platform.github.io/. The platform requires a minimum of 4 GB of RAM.
…
Peer reviewed Historical Letters
Bernardo Buarque Malte Vogl Jascha Merijn Schmitz Aleksandra Kaye | Published Thursday, May 16, 2024 | Last modified Friday, May 24, 2024A letter sending model with historically informed initial positions to reconstruct communication and archiving processes in the Republic of Letters, the 15th to 17th century form of scholarship.
The model is aimed at historians, willing to formalize historical assumptions about the letter sending process itself and allows in principle to set heterogeneous social roles, e.g. to evaluate the role of gender or social status in the formation of letter exchange networks. The model furthermore includes a pruning process to simulate the loss of letters to critically asses the role of biases e.g. in relation to gender, geographical regions, or power structures, in the creation of empirical letter archives.
Each agent has an initial random topic vector, expressed as a RGB value. The initial positions of the agents are based on a weighted random draw based on data from [2]. In each step, agents generate two neighbourhoods for sending letters and potential targets to move towards. The probability to send letters is a self-reinforcing process. After each sending the internal topic of the receiver is updated as a movement in abstract space by a random amount towards the letters topic.
…
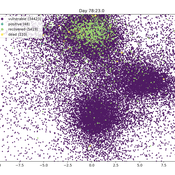
Ornstein-Uhlenbeck Pandemic package
Peter Cotton | Published Friday, April 24, 2020 | Last modified Friday, May 08, 2020Pandemic (pip install pandemic)
An agent model in which commuting, compliance, testing and contagion parameters drive infection in a population of thousands of millions. Agents follow Ornstein-Uhlenbeck processes in the plane and collisions drive transmission. Results are stored at SwarmPrediction.com for further analysis, and can be retrieved by anyone.
This is a very simple simulation that in a special case can be shown to be approximated by a compartmental model with time varying infection rate.
MERCURY extension: transport-cost
Tom Brughmans | Published Monday, July 23, 2018This is extended version of the MERCRUY model (Brughmans 2015) incorporates a ‘transport-cost’ variable, and is otherwise unchanged. This extended model is described in this publication: Brughmans, T., 2019. Evaluating the potential of computational modelling for informing debates on Roman economic integration, in: Verboven, K., Poblome, J. (Eds.), Structural Determinants in the Roman World.
Brughmans, T., 2015. MERCURY: an ABM of tableware trade in the Roman East. CoMSES Comput. Model Libr. URL https://www.comses.net/codebases/4347/releases/1.1.0/
A Simulation of Entrepreneurial Spawning
Mark Bagley | Published Wednesday, June 08, 2016 | Last modified Friday, June 30, 2017Industrial clustering patterns are the result of an entrepreneurial process where spinoffs inherit the ideas and attributes of their parent firms. This computational model maps these patterns using abstract methodologies.
Model of Context Switching with Segregation
Davide Nunes | Published Thursday, August 02, 2012 | Last modified Saturday, April 27, 2013In the context switching model, a society of agents embedded in multiple social relations, engages in a simple abstract game: the consensus game. Each agent has to choose towards one of two possible choices which are basically arbitrary. The objective of the game is to reach a global consensus, but the particular choice that gets collectively selected is irrelevant.
FOUR SEASONS
Lars G Spang | Published Tuesday, March 28, 2017Butterflies (turtles) goes through metamorphism and moves to corresponding patches each season of the year. The number of years and seasons are monitored.
06 EiLab V1.36 – Entropic Index Laboratory
Garvin Boyle | Published Saturday, January 31, 2015 | Last modified Friday, April 14, 2017EiLab explores the role of entropy in simple economic models. EiLab is one of several models exploring the dynamics of sustainable economics – PSoup, ModEco, EiLab, OamLab, MppLab, TpLab, and CmLab.
Displaying 10 of 1123 results for "Bin-Tzong Chi" clear search