About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 69 results space clear search
Peer reviewed Applying Brantingham’s Neutral Model of Stone Raw Material Procurement to the Pinnacle Point Middle Stone Age Record, Western Cape, South Africa
Marco Janssen Simen Oestmo Haley Cawthra | Published Sunday, March 10, 2019This model is an application of Brantingham’s neutral model to a real landscape with real locations of potential sources. The sources are represented as their sizes during current conditions, and from marine geophysics surveys, and the agent starts at a random location in Mossel Bay Region (MBR) surrounding the Archaeological Pinnacle Point (PP) locality, Western Cape, South Africa. The agent moves at random on the landscape, picks up and discards raw materials based only upon space in toolkit and probability of discard. If the agent happens to encounter the PP locality while moving at random the agent may discard raw materials at it based on the discard probability.
The impact of potential crowd behaviours on emergency evacuation: an evolutionary game theoretic approach
Azhar Mohd Ibrahim | Published Monday, July 30, 2018Crowd dynamics have important applications in evacuation management systems relevant to organizing safer large scale gatherings. For crowd safety, it is very important to study the evolution of potential crowd behaviours by simulating the crowd evacuation process. Planning crowd control tasks by studying the impact of crowd behaviour evolution towards evacuation could mitigate the possibility of crowd disasters. During a typical emergency evacuation scenario, conflict among agents occurs when agents intend to move to the same location as a result of the interaction with their nearest neighbours. The effect of the agent response towards their neighbourhood is vital in order to understand the effect of variation of crowd behaviour on the whole environment. In this work, we model crowd motion subject to exit congestion under uncertainty conditions in a continuous space via computer simulations. We model best-response, risk-seeking, risk-averse and risk-neutral behaviours of agents via certain game theoretic notions. We perform computer simulations with heterogeneous populations in order to study the effect of the evolution of agent behaviours towards egress flow under threat conditions. Our simulation results show the relation between the local crowd pressure and the number of injured agents. We observe that when the proportion of agents in a population of risk-seeking agents is increased, the average crowd pressure, average local density and the number of injured agents increases. Besides that, based on our simulation results, we can infer that crowd disasters could be prevented if the agent population consists entirely of risk-averse and risk-neutral agents despite circumstances that lead to threats.
How does knowledge infrastructure mobilization influence the safe operating space of regulated exploited ecosystems?
Jean-Denis Mathias | Published Tuesday, July 17, 2018Decision-makers often have to act before critical times to avoid the collapse of ecosystems using knowledge \textcolor{red}{that can be incomplete or biased}. Adaptive management may help managers tackle such issues. However, because the knowledge infrastructure required for adaptive management may be mobilized in several ways, we study the quality and the quantity of knowledge provided by this knowledge infrastructure. In order to analyze the influence of mobilized knowledge, we study how the following typology of knowledge and its use may impact the safe operating space of exploited ecosystems: 1) knowledge of the past based on a time series distorted by measurement errors; 2) knowledge of the current systems’ dynamics based on the representativeness of the decision-makers’ mental models of the exploited ecosystem; 3) knowledge of future events based on decision-makers’ likelihood estimates of extreme events based on modeling infrastructure (models and experts to interpret them) they have at their disposal. We consider different adaptive management strategies of a general regulated exploited ecosystem model and we characterize the robustness of these strategies to biased knowledge. Our results show that even with significant mobilized knowledge and optimal strategies, imperfect knowledge may still shrink the safe operating space of the system leading to the collapse of the system. However, and perhaps more interestingly, we also show that in some cases imperfect knowledge may unexpectedly increase the safe operating space by suggesting cautious strategies.
The code enables to calculate the safe operating spaces of different managers in the case of biased and unbiased knowledge.
Peer reviewed Strategy with Externalities
J M Applegate Glenn Hoetker | Published Thursday, December 21, 2017The SWE models firms search behaviour as the performance landscape shifts. The shift represents society’s pricing of negative externalities, and the performance landscape is an NK structure. The model is written in NetLogo.
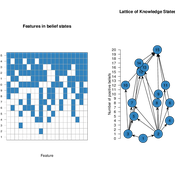
Knowledge Space Model for Opinion Dynamics
Shane Mueller | Published Thursday, September 28, 2017 | Last modified Thursday, September 20, 2018Knowledge Space model of Opinion Dynamics.
Extended Flache and Mas (2008)
Hadi Aliahmadi | Published Wednesday, August 16, 2017 | Last modified Monday, February 26, 2018We extend the Flache-Mäs model to incorporate the location and dyadic communication regime of the agents in the opinion formation process. We make spatially proximate agents more likely to interact with each other in a pairwise communication regime.
TERRoir level Organic matter Interactions and Recycling model
Myriam Grillot | Published Wednesday, April 19, 2017 | Last modified Wednesday, June 17, 2020The TERROIR agent-based model was built for the multi-level analysis of biomass and nutrient flows within agro-sylvo-pastoral villages in West Africa. It explicitly takes into account both human organization and spatial extension of such flows.
A social network model to analyze team assembly mechanisms
Andreas Koch | Published Monday, April 10, 2017This model simulates networking mechanisms of an empirical social network. It correlates event determinants with place-based geography and social capital production.
From Cyber Space Opinion Leaders and the Spread of Anti-Vaccine Extremism to Physical Space Disease Outbreaks
Xiaoyi Yuan | Published Wednesday, March 08, 2017 | Last modified Friday, March 31, 2017This model simulates the spread of anti-vaccine sentiments in cyber and physical space and how it creates emergence of clusters of anti-vacciners, which eventually lead to higher probablity of disease outbreaks.
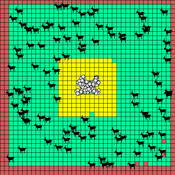
HomininSpace
Fulco Scherjon | Published Friday, November 25, 2016 | Last modified Tuesday, October 06, 2020A modelling system to simulate Neanderthal demography and distribution in a reconstructed Western Europe for the late Middle Paleolithic.
Displaying 10 of 69 results space clear search