About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 360 results for "John C Moore" clear search
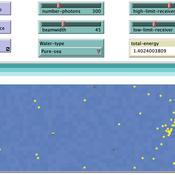
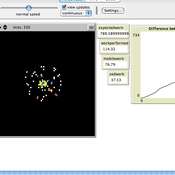
ABM for Underwater optical wireless communication in a water tank
Mohamed ABID | Published Sunday, May 29, 2022This model simulates the propagation of photons in a water tank. A source of light emits an impulse of photons with equal energy represented by yellow dots. These photons are then scattered by water particles before possibly reaching the photo-detector represented by a gray line. Different types of water are considered. For each one of them we calculate the total received energy.
The water tank is represented by a blue rectangle with fixed dimensions. It’s exposed to the air interface and has totally absorbent barriers. Four types of water are supported. Each one is characterized by its absorption and scattering coefficients.
At the source, the photons are generated uniformly with a random direction within the beamwidth. Each photon travels a random distance drawn from a distribution depending on the water characteristics before encountering a water particle.
Based on the updated position of the photon, three situations may occur:
-The photon hits the barrier of the tank on its trajectory. In this case it’s considered as lost since the barriers are assumed totally absorbent.
…
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
Parental choices, children's skills, and skill inequality: An agent-based model implemented in Python
Andrés Cardona | Published Thursday, October 30, 2014The model explores the emergence of inequality in cognitive and socio-emotional skills at the societal level within and across generations that results from differences in parental investment behavior during childhood and adolescence.
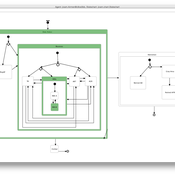
Life Cycle Cost of Military Manpower Model
Jonathan Ozik Todd Combs | Published Monday, January 05, 2015We demonstrate how Repast Simphony statecharts can efficiently encapsulate the deep classification hierarchy of the U.S. Air Force for manpower life cycle costing.
Peer reviewed Lithic Raw Material Procurement and Provisioning
Jonathan Paige | Published Friday, March 06, 2015 | Last modified Thursday, March 12, 2015This model simulates the lithic raw material use and provisioning behavior of a group that inhabits a permanent base camp, and uses stone tools.
Exploring organizational learning in innovation networks. An agent-based model
Sandra Schmid | Published Saturday, March 07, 2015This agent-based model represents a stylized inter-organizational innovation network where firms collaborate with each other in order to generate novel organizational knowledge.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
HomininSpace
Fulco Scherjon | Published Friday, November 25, 2016 | Last modified Tuesday, October 06, 2020A modelling system to simulate Neanderthal demography and distribution in a reconstructed Western Europe for the late Middle Paleolithic.
Climate Change Adaptation in Coastal Regions
Emma Cutler | Published Thursday, June 01, 2017This generic model simulates climate change adaptation in the form of resistance, accommodation, and retreat in coastal regions vulnerable to sea level rise and flooding. It tracks how population changes as households retreat to higher ground.
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
Displaying 10 of 360 results for "John C Moore" clear search