About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 74 results for "Suzan L Lapp" clear search
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
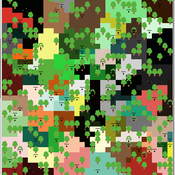
Community Forest Management with Monitoring and Sanctioning
Maya Lapp Colby Long | Published Wednesday, April 29, 2020 | Last modified Friday, July 23, 2021This NetLogo ABM builds on Elena Vallino’s model of Loggers using community-based natural resource management for a forest ecosystem. In it we introduce an alternative mechanism for Logger cheating and enforcement of CBNRM rules.
Agent-based model of risk behavior in adolescence
N Schuhmacher P Van Geert L Ballato | Published Monday, June 24, 2013 | Last modified Monday, April 08, 2019The computer model simulates the development of a social network (i.e. formation of friendships and cliques), the (dyadic) interactions between pupils and the development of similarities and differences in their behavioral profiles.
Rebel Group Protection Rackets
Gerd Wagner Luis Gustavo Nardin Kamil C. Klosek Frances Duffy | Published Wednesday, December 04, 2019System Narrative
How do rebel groups control territory and engage with the local economy during civil war? Charles Tilly’s seminal War and State Making as Organized Crime (1985) posits that the process of waging war and providing governance resembles that of a protection racket, in which aspiring governing groups will extort local populations in order to gain power, and civilians or businesses will pay in order to ensure their own protection. As civil war research increasingly probes the mechanisms that fuel local disputes and the origination of violence, we develop an agent-based simulation model to explore the economic relationship of rebel groups with local populations, using extortion racket interactions to explain the dynamics of rebel fighting, their impact on the economy, and the importance of their economic base of support. This analysis provides insights for understanding the causes and byproducts of rebel competition in present-day conflicts, such as the cases of South Sudan, Afghanistan, and Somalia.
Model Description
The model defines two object types: RebelGroup and Enterprise. A RebelGroup is a group that competes for power in a system of anarchy, in which there is effectively no government control. An Enterprise is a local civilian-level actor that conducts business in this environment, whose objective is to make a profit. In this system, a RebelGroup may choose to extort money from Enterprises in order to support its fighting efforts. It can extract payments from an Enterprise, which fears for its safety if it does not pay. This adds some amount of money to the RebelGroup’s resources, and they can return to extort the same Enterprise again. The RebelGroup can also choose to loot the Enterprise instead. This results in gaining all of the Enterprise wealth, but prompts the individual Enterprise to flee, or leave the model. This reduces the available pool of Enterprises available to the RebelGroup for extortion. Following these interactions the RebelGroup can choose to AllocateWealth, or pay its rebel fighters. Depending on the value of its available resources, it can add more rebels or expel some of those which it already has, changing its size. It can also choose to expand over new territory, or effectively increase its number of potential extorting Enterprises. As a response to these dynamics, an Enterprise can choose to Report expansion to another RebelGroup, which results in fighting between the two groups. This system shows how, faced with economic choices, RebelGroups and Enterprises make decisions in war that impact conflict and violence outcomes.
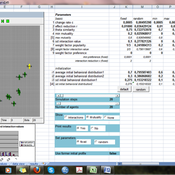
Peer reviewed BAM: The Bottom-up Adaptive Macroeconomics Model
Alejandro Platas López Alejandro Guerra-Hernández | Published Tuesday, January 14, 2020 | Last modified Sunday, July 26, 2020Overview
Purpose
Modeling an economy with stable macro signals, that works as a benchmark for studying the effects of the agent activities, e.g. extortion, at the service of the elaboration of public policies..
…
Mobility, Ethnicity, and Language-Based Immigrant Settlement Model - MELBIS
Liliana Perez Jonathan Gaudreau Suzana Dragicevic Taylor Anderson Aaron Leung | Published Monday, June 14, 2021 | Last modified Monday, June 14, 2021MELBIS-V1 is a spatially explicit agent-based model that allows the geospatial simulation of the decision-making process of newcomers arriving in the bilingual cities and boroughs of the island of Montreal, Quebec in CANADA, and the resulting urban segregation spatial patterns. The model was implemented in NetLogo, using geospatial raster datasets of 120m spatial resolution.
MELBIS-V2 enhances MELBIS-V1 to implement and simulate the decision-making processes of incoming immigrants, and to analyze the resulting spatial patterns of segregation as immigrants arrive and settle in various cities in Canada. The arrival and segregation of immigrants is modeled with MELBIS-V2 and compared for three major Canadian immigration gateways, including the City of Toronto, Metro Vancouver, and the City of Calgary.
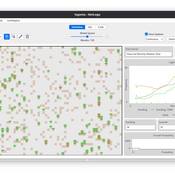
A network agent-based model of ethnocentrism and intergroup cooperation
Ross Gore | Published Sunday, October 27, 2019We present a network agent-based model of ethnocentrism and intergroup cooperation in which agents from two groups (majority and minority) change their communality (feeling of group solidarity), cooperation strategy and social ties, depending on a barrier of “likeness” (affinity). Our purpose was to study the model’s capability for describing how the mechanisms of preexisting markers (or “tags”) that can work as cues for inducing in-group bias, imitation, and reaction to non-cooperating agents, lead to ethnocentrism or intergroup cooperation and influence the formation of the network of mixed ties between agents of different groups. We explored the model’s behavior via four experiments in which we studied the combined effects of “likeness,” relative size of the minority group, degree of connectivity of the social network, game difficulty (strength) and relative frequencies of strategy revision and structural adaptation. The parameters that have a stronger influence on the emerging dominant strategies and the formation of mixed ties in the social network are the group-tag barrier, the frequency with which agents react to adverse partners, and the game difficulty. The relative size of the minority group also plays a role in increasing the percentage of mixed ties in the social network. This is consistent with the intergroup ties being dependent on the “arena” of contact (with progressively stronger barriers from e.g. workmates to close relatives), and with measures that hinder intergroup contact also hindering mutual cooperation.
Agent-Based Model for Multiple Team Membership (ABMMTM)
Andrew Collins | Published Thursday, April 03, 2025The Agent-Based Model for Multiple Team Membership (ABMMTM) simulates design teams searching for viable design solutions, for a large design project that requires multiple design teams that are working simultaneously, under different organizational structures; specifically, the impact of multiple team membership (MTM). The key mechanism under study is how individual agent-level decision-making impacts macro-level project performance, specifically, wage cost. Each agent follows a stochastic learning approach, akin to simulated annealing or reinforcement learning, where they iteratively explore potential design solutions. The agent evaluates new solutions based on a random-walk exploration, accepting improvements while rejecting inferior designs. This iterative process simulates real-world problem-solving dynamics where designers refine solutions based on feedback.
As a proof-of-concept demonstration of assessing the macro-level effects of MTM in organizational design, we developed this agent-based simulation model which was used in a simulation experiment. The scenario is a system design project involving multiple interdependent teams of engineering designers. In this scenario, the required system design is split into three separate but interdependent systems, e.g., the design of a satellite could (trivially) be split into three components: power source, control system, and communication systems; each of three design team is in charge of a design of one of these components. A design team is responsible for ensuring its proposed component’s design meets the design requirement; they are not responsible for the design requirements of the other components. If the design of a given component does not affect the design requirements of the other components, we call this the uncoupled scenario; otherwise, it is a coupled scenario.
WEEM (Woodlot Establishment and Expansion Model)
Jürgen Groeneveld Vianny Ahimbisibwe Uta Berger Melvin Lippe Susan Balaba Tumwebaze Eckhard Auch | Published Monday, September 27, 2021The agent-based model WEEM (Woodlot Establishment and Expansion Model) as described in the journal article, has been designed to make use of household socio-demographics (household status, birth, and death events of households), to better understand the temporal dynamics of woodlot in the buffer zones of Budongo protected forest reserve, Masindi district, Uganda. The results contribute to a mechanistic understanding of what determines the current gap between intention and actual behavior in forest land restoration at farm level.
Logônia: Plant Growth Response Model in NetLogo
Leandro Garcia Daniel Vartanian Aline | Published Saturday, September 13, 2025 | Last modified Tuesday, September 16, 2025Logônia is a NetLogo model that simulates the growth response of a fictional plant, logônia, under different climatic conditions. The model uses climate data from WorldClim 2.1 and demonstrates how to integrate the LogoClim model through the LevelSpace extension.
Logônia follows the FAIR Principles for Research Software (Barker et al., 2022) and is openly available on the CoMSES Network and GitHub.
Displaying 10 of 74 results for "Suzan L Lapp" clear search