About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 27 results for "Johannes Weyer" clear search
DITCH --- A Model of Inter-Ethnic Partnership Formation
Ruth Meyer Laurence Lessard-Phillips Huw Vasey | Published Wednesday, November 05, 2014 | Last modified Tuesday, February 02, 2016The DITCH model has been developed to investigate partner selection processes, focusing on individual preferences, opportunities for contact, and group size to uncover how these may lead to differential rates of inter-ethnic marriage.
SimPLS - The PLS Agent
Iris Lorscheid Sandra Schubring Matthias Meyer Christian Ringle | Published Monday, April 18, 2016 | Last modified Tuesday, May 17, 2016The simulation model SimPLS shows an application of the PLS agent concept, using SEM as empirical basis for the definition of agent architectures. The simulation model implements the PLS path model TAM about the decision of using innovative products.
epiworldR Type: Fast Agent-Based Epi Models
George G. Vega Yon Derek Meyer | Published Monday, August 26, 2024A flexible framework for Agent-Based Models (ABM), the ‘epiworldR’ package provides methods for prototyping disease outbreaks and transmission models using a ‘C++’ backend, making it very fast. It supports multiple epidemiological models, including the Susceptible-Infected-Susceptible (SIS), Susceptible-Infected-Removed (SIR), Susceptible-Exposed-Infected-Removed (SEIR), and others, involving arbitrary mitigation policies and multiple-disease models. Users can specify infectiousness/susceptibility rates as a function of agents’ features, providing great complexity for the model dynamics. Furthermore, ‘epiworldR’ is ideal for simulation studies featuring large populations.
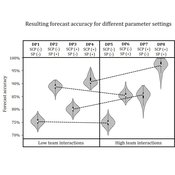
Demand Planning Model
Iris Lorscheid Jonas Hauke Matthias Meyer | Published Wednesday, October 04, 2017Demand planning requires processing of distributed information. In this process, individuals, their properties and interactions play a crucial role. This model is a computational testbed to investigate these aspects with respect to forecast accuracy.
An agent-based simulation of discussion processes in risk workshops
Matthias Meyer Clemens Harten Lucia Bellora-Bienengräber | Published Thursday, September 30, 2021The model measures drivers of effectiveness of risk assessments in risk workshops regarding the correctness and required time. Specifically, we model the limits to information transfer, incomplete discussions, group characteristics, and interaction patterns and investigate their effect on risk assessment in risk workshops.
The model simulates a discussion in the context of a risk workshop with 9 participants. The participants use Bayesian networks to assess a given risk individually and as a group.
Agent-based simulation of discussion processes in risk workshops with quantitative skepticism
Matthias Meyer Clemens Harten Lucia Bellora-Bienengräber | Published Sunday, August 14, 2022The model measures drivers of effectiveness of risk assessments in risk workshops where a calculative culture of quantitative skepticism is present. We model the limits to information transfer, incomplete discussions, group characteristics, and interaction patterns and investigate their effect on risk assessment in risk workshops, in order to contrast results to a previous model focused on a calculative culture of quantitative enthusiasm.
The model simulates a discussion in the context of a risk workshop with 9 participants. The participants use constraint satisfaction networks to assess a given risk individually and as a group.
Peer reviewed Descriptive Norm and Fraud Dynamics
Alexandra Eckert Matthias Meyer Christian Stindt | Published Tuesday, January 07, 2025 | Last modified Tuesday, March 24, 2026The “Descriptive Norm and Fraud Dynamics” model demonstrates how fraudulent behavior can either proliferate or be contained within non-hierarchical organizations, such as peer networks, through social influence taking the form of a descriptive norm. This model expands on the fraud triangle theory, which posits that an individual must concurrently possess a financial motive, perceive an opportunity, and hold a pro-fraud attitude to engage in fraudulent activities (red agent). In the absence of any of these elements, the individual will act honestly (green agent).
The model explores variations in a descriptive norm mechanism, ranging from local distorted knowledge to global perfect knowledge. In the case of local distorted knowledge, agents primarily rely on information from their first-degree colleagues. This knowledge is often distorted because agents are slow to update their empirical expectations, which are only partially revised after one-to-one interactions. On the other end of the spectrum, local perfect knowledge is achieved by incorporating a secondary source of information into the agents’ decision-making process. Here, accurate information provided by an observer is used to update empirical expectations.
The model shows that the same variation of the descriptive norm mechanism could lead to varying aggregate fraud levels across different fraud categories. Two empirically measured norm sensitivity distributions associated with different fraud categories can be selected into the model to see the different aggregate outcomes.
Team Cognition
Iris Lorscheid | Published Sunday, May 23, 2021The teamCognition model investigates team decision processes by using an agent-based model to conceptualize team decisions as an emergent property. It uses a mixed-method research design with a laboratory experiment providing qualitative and quantitative input for the model’s construction, as well as data for an output validation of the model. The agent-based model is used as a computational testbed to contrast several processes of team decision making, representing potential, simplified mechanisms of how a team decision emerges. The increasing overall fit of the simulation and empirical results indicates that the modeled decision processes can at least partly explain the observed team decisions.
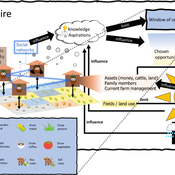
3spire: an agent-based model for exploring aspiration adaptation theory and its implications on smallholder farmers in Ethiopia
ateeuw Yue Dou Markus A Meyer Andrew Nelson | Published Sunday, February 16, 20253spire is an ABM where farming households make management decisions aimed at satisficing along the aspirational dimensions: food self-sufficiency, income, and leisure. Households decision outcomes depend on their social networks, knowledge, assets, household needs, past management, and climate/market trends
AMIRIS
Ulrich Frey Felix Nitsch Christoph Schimeczek Johannes Kochems Kristina Nienhaus Evelyn Sperber Aboubakr Achraf El Ghazi Seyedfarzad Sarfarazi | Published Thursday, February 03, 2022AMIRIS is the Agent-based Market model for the Investigation of Renewable and Integrated energy Systems.
It is an agent-based simulation of electricity markets and their actors.
AMIRIS enables researches to analyse and evaluate energy policy instruments and their impact on the actors involved in the simulation context.
Different prototypical agents on the electricity market interact with each other, each employing complex decision strategies.
AMIRIS allows to calculate the impact of policy instruments on economic performance of power plant operators and marketers.
…
Displaying 10 of 27 results for "Johannes Weyer" clear search